By Cory Bennett and Eric Geller
Cory Bennett is the editor of POLITICO Pro Cybersecurity. Eric Geller covers cybersecurity for Politico Pro. He joined Politico in June 2016 after two years at the Daily Dot, where he covered technology policy and soon grew to realize that cyber was his passion. Eric grew up just outside of Washington, D.C., and graduated from Kenyon College in 2014 with a degree in political science. Besides cybersecurity, his interests include Star Wars and bad puns.
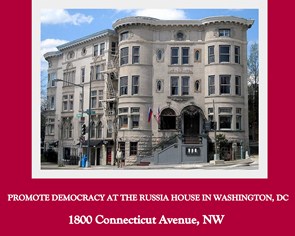
Inaccuracies in reporting cyberattacks can only sow doubts about Moscow's capability with people who are already skeptical about Russian attempts to influence the U.S. election. | AP Photo
The Obama administration’s efforts to press its election-hacking accusations against Russia could be undermined by a flurry of unfounded cyber charges against Moscow.
The Obama administration has a new problem with its high-profile smackdown of Russia for cyberattacks: False positives.
The hyped — and quickly deflated — news reports alleging Kremlin-backed hacking of the U.S. electric grid via a Vermont power company have stoked fears among cyber specialists that a flurry of false accusations against Russia will follow, as U.S. companies respond to the administration's request that they search for possible Russian-linked cyberattacks on their systems. And those easily debunked tales could sow doubts about all hacking allegations against Russia — undermining the administration's arguments that it has solid evidence Vladimir Putin's regime used digital mischief to interfere in the 2016 presidential election.
False positives could also play into the hands of President-elect Donald Trump, who has scoffed at the accusations about Russian election-meddling. Last week, he told reporters that "nobody knows exactly what’s going on” when it comes to cyberattacks. At the very least, it threatens to cloud the debate, said several cyber-savvy lawmakers.
"There has been some false reporting out there and obviously that kind of inflames the issue,” said House Homeland Security Chairman Michael McCaul (R-Texas), who believes Russia was behind the election hacks and has long warned of Moscow’s nefarious digital plots.
Inaccuracies in reporting cyberattacks — whether in the media, by government officials or by companies themselves — can only sow doubts about Moscow's capability with people who are already skeptical about Russian attempts to influence the U.S. election. The Vermont incident has shown this, cyber specialists argued.
"People [are] vehemently saying [about Vermont], ‘Obviously this is proof that the Obama administration faked the DNC [hack] and maybe it was an inside job,’” said Robert Lee, a former Air Force cyber operator who now heads the digital security firm Dragos. Lee said he has received a torrent of Twitter harassment and an emailed death threat for supporting the government’s conclusions about the election despite last weekend's false positive regarding the electric grid.
"In the short term, both Trump and these false rumors are playing into Putin’s hands and undermining these last-minute actions by the Obama administration,” said Craig Varoga, a longtime Democratic strategist.
In the initial report, The Washington Post wrote that Kremlin-backed hackers had cracked into the U.S. power grid through Vermont’s Burlington Electric Department. But the utility quickly clarified that the potential infection was on a laptop not connected the grid, and that the nefarious activity detected may not even be linked to Russia.
Lawmakers and security researchers said such "false positives” about Russian hacks are inevitable, and the Vermont case will not be the last one.
"I do think there’ll be more false flags,” said Rep. John Ratcliffe (R-Texas), who chairs a cyber-focused Homeland Security Committee subpanel.
The whiplash Vermont story has played out as Obama administration officials make their final pitch to convince Congress and the public that senior Moscow officials tied to Putin's regime orchestrated a robust hacking campaign to interfere with the U.S. election.
Trump has repeatedly dismissed this assessment — despite the unanimous conclusion of every government intelligence agency — and accused Obama of hawking a politically motivated narrative to undermine his legitimacy.
"History will be quite harsh on both Trump and Putin, but in the short-term, it’s Obama who’s facing the toughest headwinds,” Varoga said.
The White House has barreled ahead with its case against Moscow.
Last week, it sanctioned Russia for the election-season hacking and ejected 35 alleged Russian spies from U.S. soil. This Thursday, the administration will send its top spy, Director of National Intelligence James Clapper, to testify before the Senate Armed Services Committee on the topic.
Before the week’s end, the administration may also release an extensive intelligence community report on election hacking spanning back to 2008 that is expected to include the most detailed recounting yet of Russia’s 2016 digital meddling.
But all that will occur against the backdrop of the false report about the Vermont power grid hack.
The uproar began Friday night, when the Post reported, citing anonymous administration officials, that a Vermont utility had discovered "code associated with the Russian hacking operation” in one of its systems. The Post described the incident as a "penetration of the nation’s electrical grid."
But the Burlington Electric Department swiftly corrected the record, saying the malware was detected "in a single laptop not connected” to the broader power grid.
"It’s unfortunate that an official or officials improperly shared inaccurate information with one media outlet, leading to multiple inaccurate reports around the country,” the department said.
As a result, "the realities of previous espionage operations have been completely overshadowed,” said John Hultquist, director of cyber espionage analysis at iSIGHT Partners, a division of top security firm FireEye.
To cybersecurity experts, the larger blame rests with a joint report that the FBI and the Department of Homeland Security released last week on Russian cyber activity.
The 13-page missive, issued in conjunction with last week’s sanctions, was meant to offer computer network defenders around the country some technical details that may help them uncover other Russian digital infiltrations. But experts have knocked the report, saying it included vague, misleading and worthless information for those trying to root out hackers.
"I think the specific technical indicators they did publish are out of date,” said Matt Tait, a digital security researcher who founded the U.K.-based consultancy Capital Alpha Security.
That means that as cyber professionals around the country search their systems for the digital indicators laid out in the report, they may flag old or harmless indications of Russian digital activity and mistakenly believe Moscow has gotten into their networks.
Essentially, said Lee, following the report’s directions is "just time and effort wasted.”
That appears to be what happened in Vermont.
The utility eventually downgraded the incident to merely a "specific type of Internet traffic” on the laptop — something that might even be benign, as The Post acknowledged in a follow-up story.
Cyber researchers and Democrats fear the incident could damage the Obama administration's upcoming election hacking report, preemptively giving critics ammunition.
"I think it’s going to over-politicize the report even before it comes out,” Lee said. "It adds increased pressure on it.”
"The false positive in Vermont has already been seized upon as a political issue, unfortunately,” added one researcher at a major cybersecurity firm, who requested anonymity to discuss politics. "It overshadowed some of the other realities of Russian cyber activity.”
From a public perception standpoint, Varoga said, the incident "makes it look like all the hacking reports might be false after all.”
The apparent government leak of the initial, incorrect details about the Vermont incident could also erode years of efforts to build trust with businesses about the sharing of information on cyberattacks.
Companies have long been hesitant to give the government details about intrusions, fearing the information will wind up in the press or spark a federal investigation. The administration worked for years with Congress and industry groups to get a 2015 law passed that gives companies legal liability when sharing specifics about hacking threats.
Lee said that when his company analyzes private firms’ cyber vulnerabilities, "they do not share with the government because they know it will get leaked or get out or become political.”
The cyber researcher at a top firm added that "the fact that this went public so quickly is only going to create more problems for sharing, which is crucial for success.”
The top lobbying group for investor-owned electric utilities insisted otherwise, saying the Vermont incident will not deter them from working with the government.
"[W]hile none of us likes seeing this stuff play out in the media, there remains a sense of duty to share for the greater good, and I don't imagine that is going to change simply because of the way this played out,” said Scott Aaronson, the Edison Electric Institute’s executive director of security and business continuity.
Meanwhile, Democrats believe that these false reports are merely a blip, though some conceded that Trump may score political points with the backtracked reporting on the Vermont utility.
"Using the Vermont mistake might yield a short-term gain, but the longer term problem isn’t going to go away because he scores a political point,” said Anita Dunn, who served as White House communications director in the early part of President Barack Obama’s first term. "And in the process of scoring a short-term political point, he could undermine longer-term strategic goals his administration may end up needing to pursue in this area.”



_jpg/250px-ElbeDay1945_(NARA_ww2-121).jpg)